
Cybersecurity Management: A Survival Guide
- On May 14, 2021
Industrial Control System (ICS) is a general term that encompasses several types of control systems, including Supervisory Control and Data Acquisition (SCADA) systems, Distributed Control Systems (DCS), and other control system configurations such as skid-mounted Programmable Logic Controllers (PLC) often found in the industrial sectors and critical infrastructures. ICS are typically used in industries such as electrical, water and wastewater, oil and natural gas, chemical, transportation, pharmaceutical, pulp and paper, food and beverage, and discrete manufacturing (e.g., automotive, aerospace, and durable goods.) These control systems are essential to the operation of the Critical Infrastructures that are often highly interconnected and mutually dependent systems.
The most critical and sensitive data of Critical Infrastructures is hosted in their Industrial control system (ICS). Degradation, interruption or impairment of their ICS has serious consequences on safety, loss of sensitive data, loss of reputation or loss of service making Cybersecurity Management one of the most important concerns.
Cybersecurity Management is an important governance and administration procedure aiming at the protection of an organization from internal and external risks that would negatively affect the achievement of its operational objectives. Specifically, in order to enhance the security controls, monitor their effective implementation and find ways for continuous improvement, the following steps are mandatory:
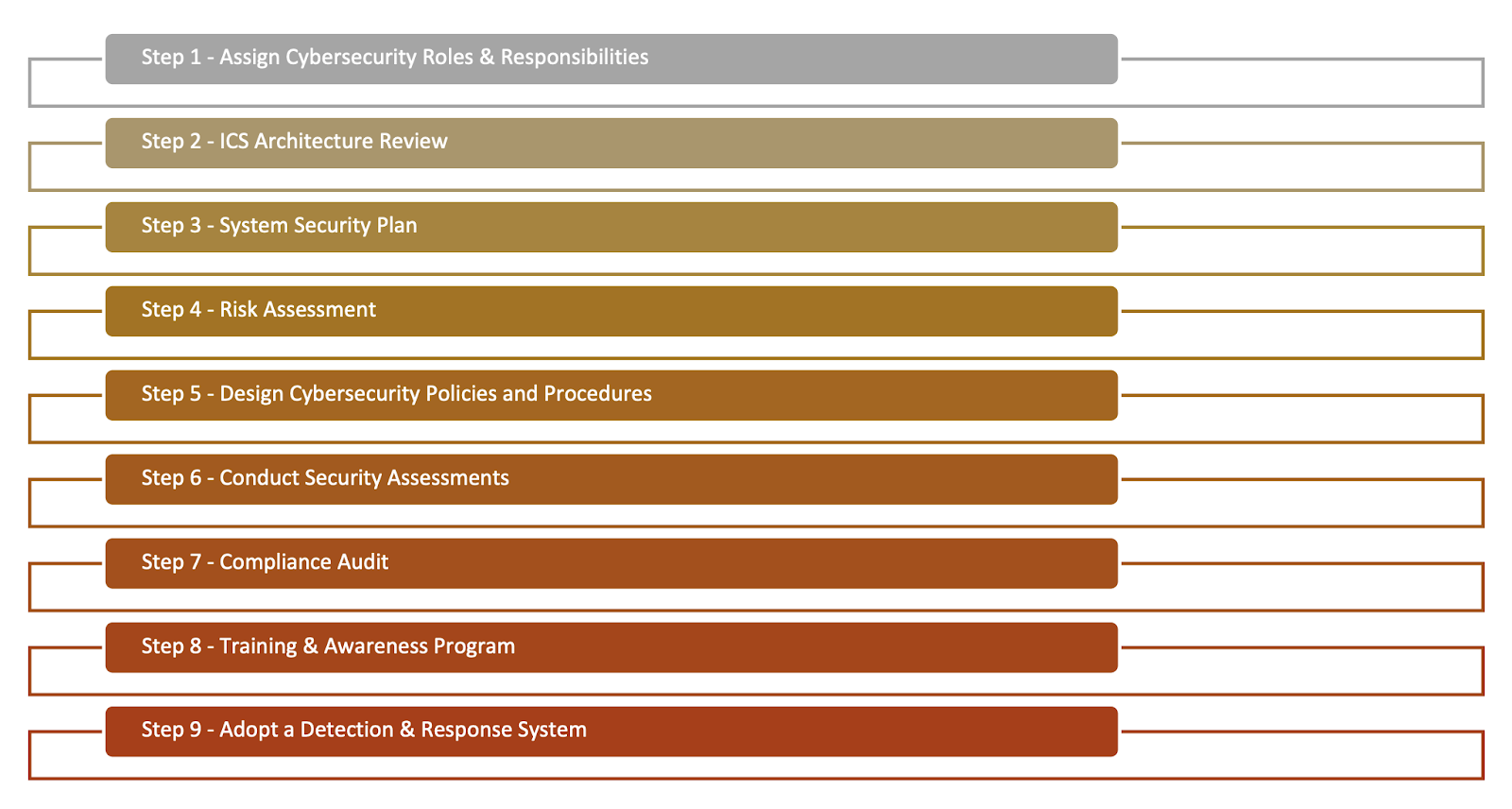
Step 1: Assign Cybersecurity Roles & Responsibilities
Appropriate roles should be defined and responsibilities should be assigned to authorized employees in order to continuously monitor the implemented cybersecurity controls ensuring continuous compliance with your Industry Cybersecurity requirements.
Step 2: ICS Architecture Review
evaluate your software, technologies, and network topology against industry best practices (i.e. NIST, SANS, ENISA) and regulatory requirements (such as NERC CIP, NIS, etc.).
Step 3: System Security Plan
Identify the criticality of the provided services; identify the consequences in case of loss of security (confidentiality, integrity, availability) of System components; identify and evaluate the potential risks that would cause significant negative consequences to the proper operation of organization business activities; and propose targeted security countermeasures.
Step 4: Risk Assessment
Identify and evaluate potential threats and vulnerabilities for each ICS asset. A series of proposed countermeasures (based on ISO 27001 and NIST) should be specified to reduce the level of risk per ICS asset.
Step 5: Design Cybersecurity Policies and Procedures
Design and implement the appropriate countermeasures by taking into account the results of the previous phases (i.e. ICS Architecture Review, System Security Plan and Risk Assessment). More specifically, the appropriate Security Policies should be specified, in order to ensure that the ICS Infrastructure complies with the industry specific cybersecurity requirements.
Step 6: Conduct Security Assessments
Evaluate the maturity of the security levels of the critical components of your ICS infrastructure. Identify your technical vulnerabilities and define the appropriate solutions in order to effectively mitigate them on time. Conduct at least once a year penetration tests, source code audits and vulnerability assessments for all critical ICS components.
Step 7: Compliance Audit
Identify the existing technical and procedural security controls as well as any grey areas that the Industry Specific Cybersecurity requirements are not properly addressed. Conduct audits in order to ensure compliance with your specific industry requirements (i.e. ISO 27001 Assessment, NERC CIP compliance audit, NIS compliance audit, NCSC guidelines for CNI, AICPA Trust Service Criteria compliance-SOC 2 Report, GDPR Assessment, etc.).
Step 8: Training & Awareness Program
The success and effectiveness of Cybersecurity depends directly on the human factor — the personnel who apply and implement the organizational and technical security controls. Hence the Company should ensure that all personnel involved with the ICS are competent in performing the required tasks on the basis of education, training, skills and experience by implementing appropriate training and awareness programs.
Step 9: Adopt a Detection & Response System
Implement a centralized logging and monitoring system in order to collect and analyze structured and unstructured security related data and telemetry from all systems, networks, and applications, generating valuable intelligence for new, emerging and advanced security threats in order to identify, analyze, predict, and prevent cyber-security threats in real time.
Want to know how you can implement these steps in your organization? 
